domain; dog; DNS Looking Glass
Today, we hyper-focus on DNS, first featuring a near-bulletproof DNS library, then a DNS client utility I cannot believe I have not dropped yet, and, finally, a neat DNS troubleshooting resource. The inspiration for this post is that we’re going to have at least one collaborative innovation event this year. You likely call them “hack weeks” or “hackathons”, but I prefer this more descriptive term since it focuses on outcomes vs. just the process. At said event, I plan to build a DNS server that uses our IP address categorization data similarly to DNS providers like Quad9 (which I highly recommend to folks who’d like to be a bit safer on the internets).
All of you dashing, talented, and clever1 subscriber-readers are no doubt intimately familiar with DNS. For those readers who may not be, this older drop has some background and links on DNS that may be helpful to at least scan before digging into today’s sections.
domain

I 💙 NLnet Labs.
They’re an independent, non-profit foundation based in the Netherlands that endeavours to make the core of the Internet a better, safer place by developing open-source software, through applied research and by promoting and contributing to open standards.
One of their most useful open-source projects is a Rust DNS library dubbed domain.
The library has a ton of batteries included:
basic data structures and functionality for creating and parsing DNS data and messages,
support for signing and verifying messages using the TSIG mechanism,
experimental support for reading data from DNS master files (also known as zone files),
experimental and as yet incomplete support for DNSSEC signing and validation,
a simple Tokio-based stub resolver.
It is straightforward to use and is one of the safer DNS library dependencies if you ever need such functionality in your projects.
dog

Benjamin Sago https://twitter.com/cairnrefinery
The dog [GH] utility is a command-line DNS client, like dig. The human-consumable output is easy on the eyes, supports traditional command-line argument syntax, and can speak in secure DNS-over-TLS and DNS-over-HTTPS protocols. Oh, it can also emit JSON — a feature that every modern CLI tool should support.
It supports at least the most common dig CLI argument formats, and would be worth adding to your “new system default install” list.
dog --json Domain_Name_System.wp.dg.cx TXT | jq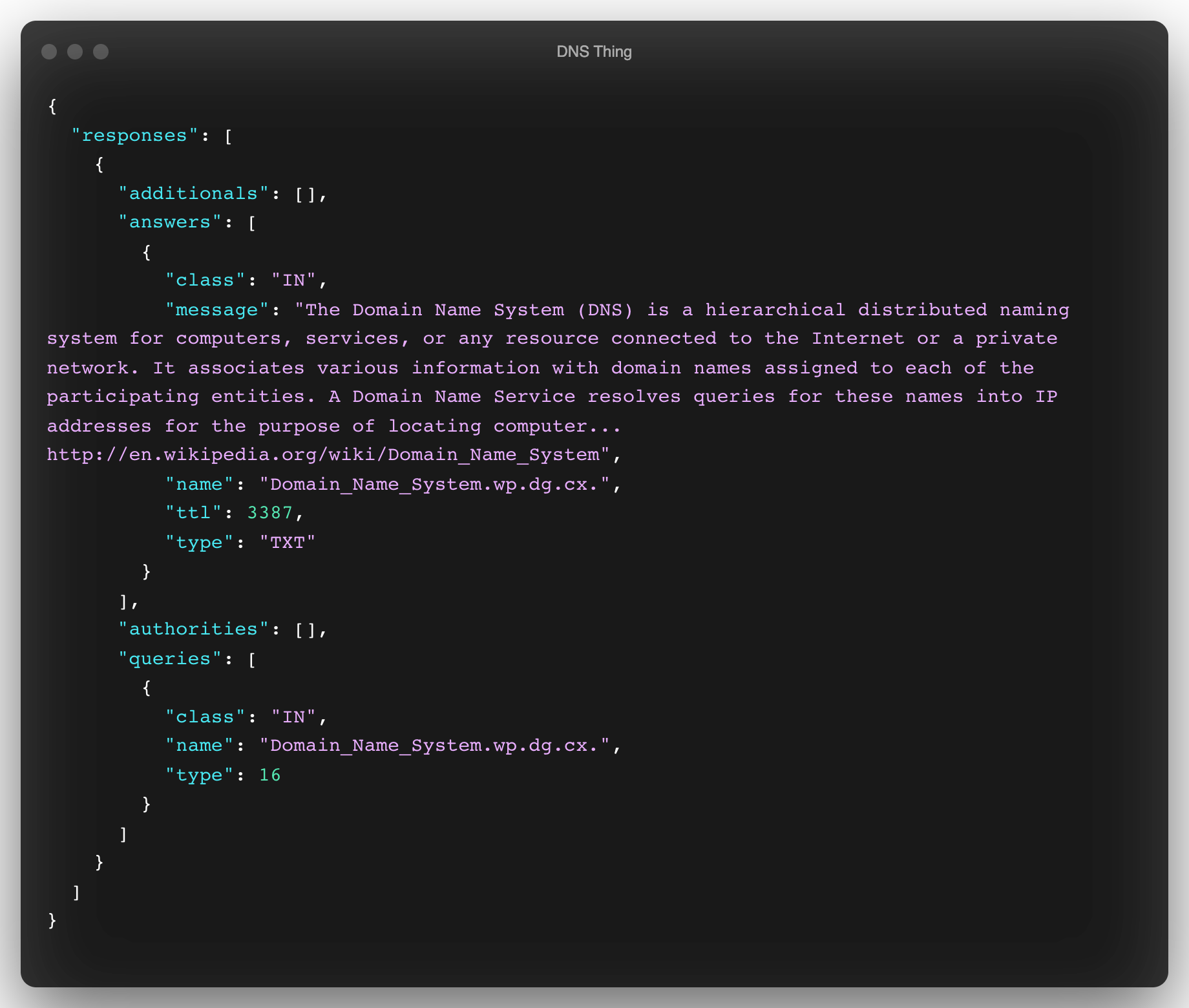
DNS Looking Glass
Tons of things can go wrong in DNS land, which is one reason why Frederic Cambus (@fcambus) built a multi-location DNS Looking Glass (DNS-LG) REST API service. (The “looking glass” name is borrowed from a service typically provided for router jockeys.)
DNS-LG can be used to verify and troubleshoot DNS propagation, geo-aware DNS servers, and Anycast DNS deployments.
Here’s how we’d test to see if we received the same result for the query in today’s midsection:
curl http://www.dns-lg.com/us01/Domain_Name_System.wp.dg.cx/txt | jq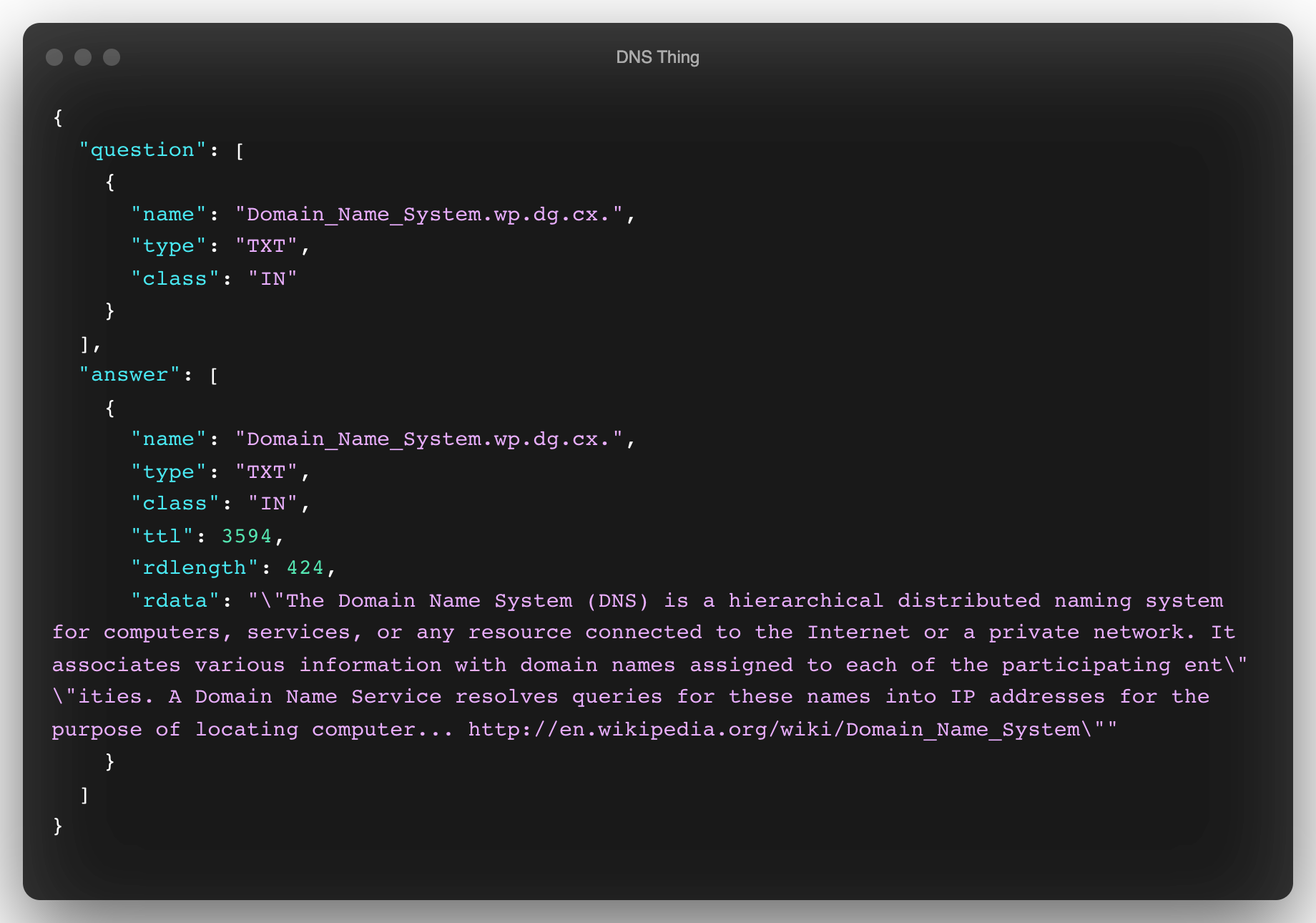
And, here’s how I’d do that in (mostly base) R for all of DNS-LG’s servers:
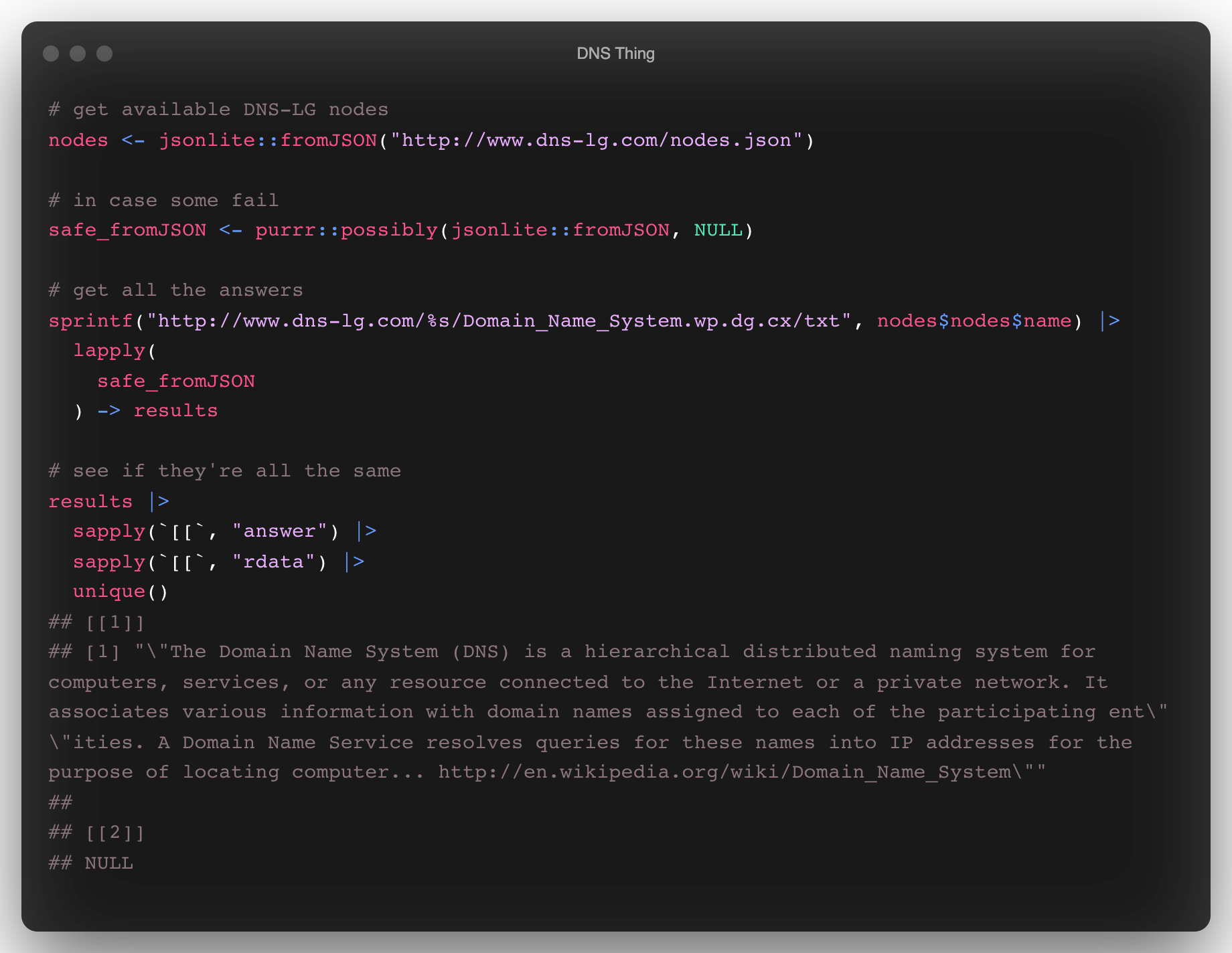
You can grab a copy of the server software and have a go at hosting your own DNS Looking Glass instance, which may be a good idea since the DNS-LG service appears to only support cleartext HTTP.
FIN
☮
Leave a comment